Managing VLAN Databases via the VLAN Trunking Protocol
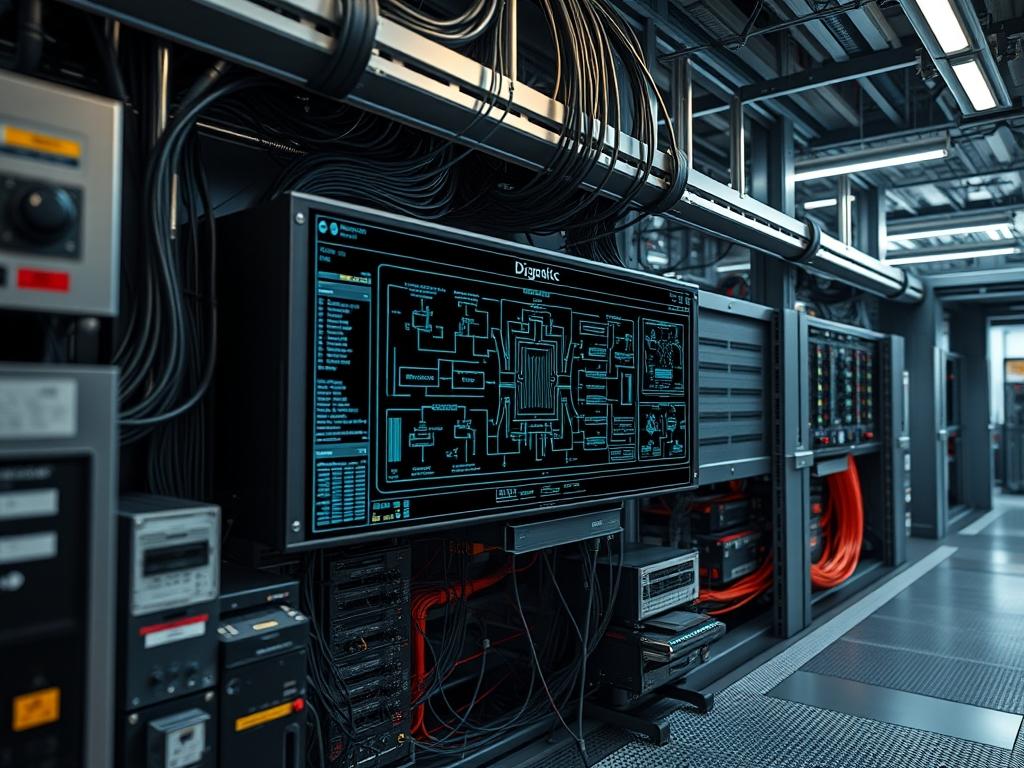
VTP VLAN Trunking serves as the structural backbone for automated Virtual Local Area Network (VLAN) management within enterprise core and distribution layers. In modern network infrastructure deployments, such as those supporting high-concurrency data centers or smart water management telemetry systems, the manual configuration of VLANs across hundreds of switches introduces significant operational risk. Configuration drift … Read more